NEXT LEVEL
SECURITY
USING YOUR TRUSTED DEVICES
SECURITY
USING YOUR TRUSTED DEVICES


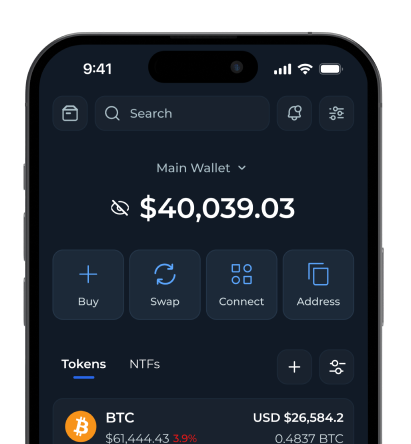
HOW TYPYCAL CRYPTO WALLETS WORK?
Single-signature wallets are dangerous
Accidentally lose your phone? Upload your private key.
Hardware wallets are clunky
Use a function to hash your private key into a Public Key and then encode that to an address.
Multi-sig wallets are painful
Seed phrase are simply the conversion of your private key into a string of words.

PRIVATE KEYS THE POINT OF FAILURE
VULTISIG is the next evolution in crypto vaults
Familiar hardware
Private keys are created in a single location

Rich hardware
Private keys exist wherever you store them. Creating a single point of failure.







 Vultisig
Vultisig